Scraped data of 500 million LinkedIn users being sold online, 2 million records leaked as proof | CyberNews
Updated on 07/04: We updated our personal data leak checker database with more than 780,000 email addresses associated with this leak. Use it to find out if your LinkedIn profile has been scraped by the threat actors.
Days after a massive Facebook data leak made the headlines, it seems like we’re in for another one, this time involving LinkedIn.
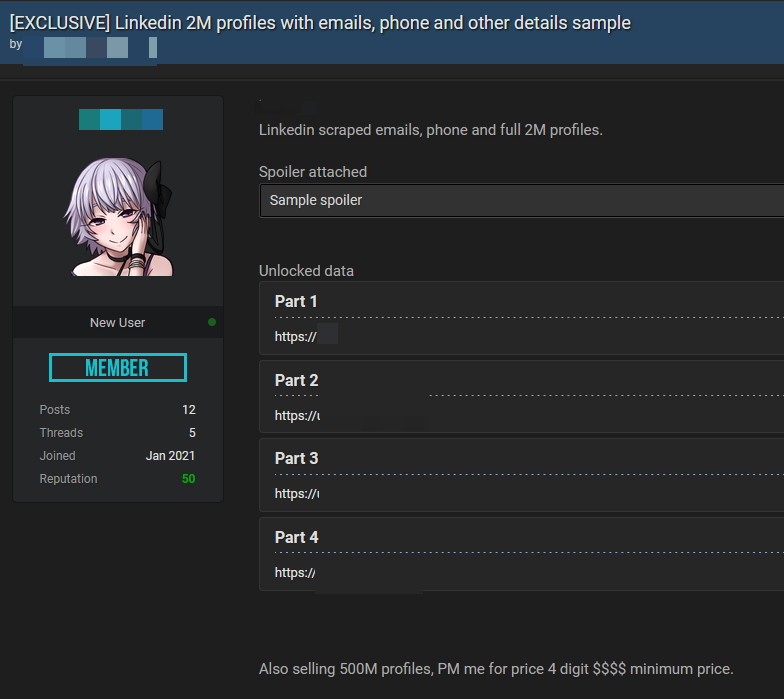
An archive containing data purportedly scraped from 500 million LinkedIn profiles has been put for sale on a popular hacker forum, with another 2 million records leaked as a proof-of-concept sample by the post author.
The four leaked files contain information about the LinkedIn users whose data has been allegedly scraped by the threat actor, including their full names, email addresses, phone numbers, workplace information, and more.
To see if your email address has been exposed in this data leak or other security breaches, use our personal data leak checker
with a library of 15+ billion breached records.
While users on the hacker forum can view the leaked samples for about $2 worth of forum credits, the threat actor appears to be auctioning the much-larger 500 million user database for at least a 4-digit sum, presumably in bitcoin.
- LinkedIn IDs
- Full names
- Email addresses
- Phone numbers
- Genders
- Links to LinkedIn profiles
- Links to other social media profiles
- Professional titles and other work-related data
An example of leaked data:
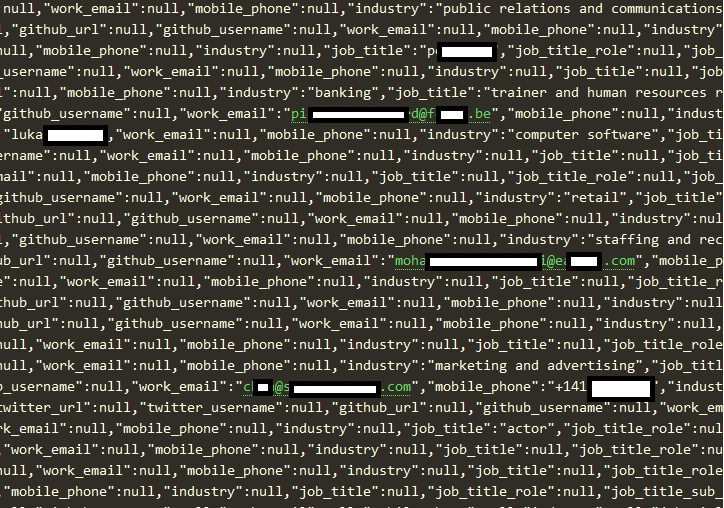
The author of the post claims that the data was scraped from LinkedIn. Our investigation team was able to confirm this by looking at the samples provided on the hacker forum. However, it’s unclear whether the threat actor is selling up-to-date LinkedIn profiles, or if the data has been taken or aggregated from a previous breach suffered by LinkedIn or other companies.
We asked LinkedIn if they could confirm that the leak was genuine, and whether they have alerted their users and clients, but we have received no reply from the company at the time of writing this report.
- Carrying out targeted phishing attacks.
- Spamming 500 million emails and phone numbers.
- Brute-forcing the passwords of LinkedIn profiles and email addresses.
What was leaked?
Based on the samples we saw from the leaked files, they appear to contain a variety of mostly professional information from LinkedIn profiles, including:
What’s the impact of the leak?
The data from the leaked files can be used by threat actors against LinkedIn users in multiple ways by:
- Use our personal data leak checker to find out if your LinkedIn data has been leaked by the threat actor.
- Beware of suspicious LinkedIn messages and connection requests from strangers.
- Change the password of your LinkedIn and email accounts.
- Consider using a password manager to create strong passwords and store them securely.
- Enable two-factor authentication (2FA) on all your online accounts.
The leaked files appear to only contain LinkedIn profile information — we did not find any deeply sensitive data like credit card details or legal documents in the sample posted by the threat actor. With that said, even an email address can be enough for a competent cybercriminal to cause real damage.
Particularly determined attackers can combine information found in the leaked files with other data breaches in order to create detailed profiles of their potential victims. With such information in hand, they can stage much more convincing phishing and social engineering attacks or even commit identity theft against the people whose information has been exposed on the hacker forum.
Originally published at https://cybernews.com

Comments
Post a Comment