- The ‘Avaddon’ group has hit AXA Asia only a week after the firm decided to stop paying ransomware actors.
- The hackers claim to have stolen 3 TB of sensitive documents from the firm and already leaked several.
- AXA threatens to create a precedent in the field, closing the tap for crooks who targeted insurance-covered firms.
Only a week ago, international insurance giant AXA decided to halt ransomware crime reimbursement in France, with the plan being to expand this strategy globally. AXA justified this by putting forth the ethical aspect of providing financial support — and thus incentive to ransomware gangs, only to see them pullulate and grow stronger.
Today, the ransomware group Avaddon has announced the victimization of the AXA Group and gives the company 240 hours to communicate and cooperate with them. If that doesn’t happen, they threaten to leak 3 TB of sensitive data, allegedly including the following:
- Customer medical reports (included HIV, hepatitis, STD, and other illness reports)
- Customer claims
- Payments to customers
- All customers IDs
- All customers bank account scanned papers
- Hospitals and doctors reserved material (private investigations for frauds, reserved agreement, denied reimbursement, contracts, reports, ID cards, etc.)
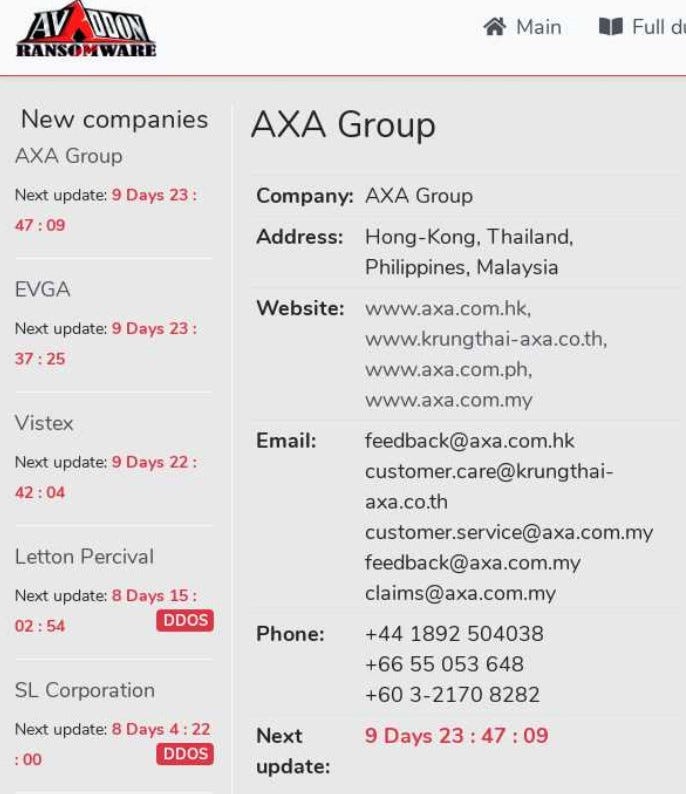
The above concern AXA Asia, comprising the company’s Thailand, Philippine, Hong Kong, and Malaysia-based operations. We have checked the corresponding websites, and they seem to be down. This could be either due to the effort of the local IT teams to contain the infection or due to DDoSing that always accompanies Avaddon’s assaults. Also, the group has leaked several sensitive documents on the extortion portal, many of which feature AXA’s letterheads and stamps, so this appears to be valid.
There is no mention of the attack being the result of AXA’s decision to stop paying ransomware actors, but no one can ignore the strong link here. It could be just a random occurrence, as ransomware groups are hitting tens of large groups every day, but the news on AXA must have drawn the attention of ransomware actors nonetheless. It is, however, improbable that attacks like this one will have any effect in changing AXA’s mind on the matter.
Experts in the field of insurance have estimated that AXA’s move will set a precedent and stated their belief that more firms will follow the same example. After all, there’s pressure from governments to stop this practice, even if paying ransomware actors remains in a gray legal area. Most importantly, though, having ransomware insurance coverage is making you a target for ransomware attacks, creating a negative incentive.
Originally published at https://www.technadu.com on May 15, 2021.

Comments
Post a Comment